The threat landscape has shifted. While DeFi protocol hacks grabbed headlines through 2023-2024, attackers in 2025-2026 have pivoted their focus to a softer target: individual wallet holders like you. Blockchain analytics firms report that personal wallet compromises now account for over 60% of stolen cryptocurrency value—a dramatic reversal from just three years ago.
The reason is simple economics. DeFi protocols have hardened their defenses with formal verification, bug bounties, and audit requirements. But millions of retail holders still store significant wealth with insufficient security practices. For sophisticated threat actors, the math favors going after many individuals rather than one well-defended protocol.
This guide provides everything you need to protect your cryptocurrency holdings in 2026. Whether you hold a few hundred dollars or several million, these practical steps will dramatically reduce your attack surface.
The 2026 Personal Wallet Threat Landscape
Before diving into defenses, understanding how attackers operate today helps you recognize threats when they appear.
Why Individuals Are Now Prime Targets
The shift from protocol attacks to personal attacks follows a clear pattern:
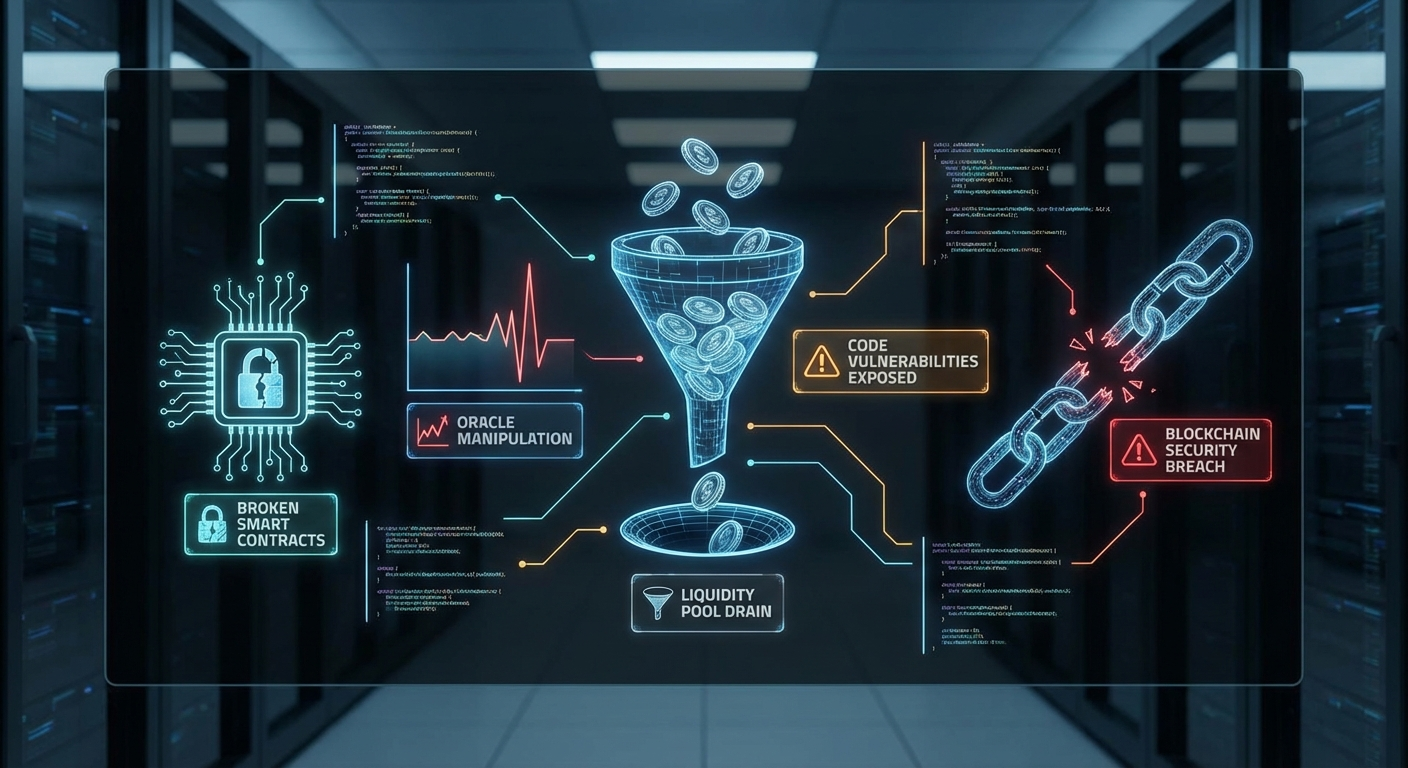
DeFi security has matured. Major protocols now undergo multiple audits, run substantial bug bounty programs, and employ formal verification. The low-hanging fruit has been picked. High-profile exploits still occur, but they require increasingly sophisticated attacks with diminishing returns.
Personal data is abundant. The 2023 Ledger customer database leak exposed over 1 million customer emails and 272,000 physical addresses. Similar breaches at other crypto companies have created comprehensive databases that attackers actively exploit. If you’ve ever purchased crypto hardware or signed up for crypto services, assume your information is compromised.
Social engineering scales efficiently. A single phishing campaign can target hundreds of thousands of wallet holders simultaneously. Even a 0.1% success rate yields significant returns when wallets can contain substantial value.
Physical attacks are increasing. The $5 wrench attack—forcing victims to transfer funds under physical threat—has moved from theoretical to documented. High-profile cases in London, Miami, Hong Kong, and Dubai demonstrate that wealthy crypto holders face real-world security risks.
Current Attack Vectors
1. Advanced Seed Phrase Phishing
Attackers have moved far beyond obvious scam emails. Current campaigns include:
- Fake firmware update notifications that direct users to cloned websites- Compromised hardware wallet unboxing videos that include subtle misdirection to phishing sites- AI-generated voice calls impersonating wallet support teams- Physical mail claiming device recalls requiring “verification” of recovery phrases- Fake recovery tools advertised to users who’ve posted about wallet issues
2. SIM Swap Attacks
Despite carrier security improvements, SIM swapping remains viable:
- Attackers social engineer or bribe carrier employees- They port your phone number to their device- They reset passwords and drain accounts using SMS-based 2FA- Average time from swap to drain: under 30 minutes
3. Supply Chain Compromises
Hardware wallet supply chains present multiple attack surfaces:
- Tampered devices sold through unofficial channels- Compromised firmware updates- Pre-generated seed phrases in “new” devices- Counterfeit devices that leak private keys
4. Clipboard Malware
Malware that silently replaces cryptocurrency addresses when you copy-paste:
- Runs invisibly in the background- Substitutes legitimate addresses with attacker-controlled ones- Particularly effective because users rarely verify full addresses
Hardware Wallet Security: Beyond the Basics
Hardware wallets remain the gold standard for crypto storage, but they’re not magic shields. Proper usage matters more than the device itself.
Choosing Your Hardware Wallet in 2026
Tier 1: Maximum Security
| Device | Key Features | Price Range |
|---|---|---|
| Ledger Stax/Flex | E-ink display, Bluetooth, Ledger Recover optional | $279-399 |
| Trezor Safe 5 | Touchscreen, Shamir Backup native, open-source | $169 |
| Keystone 3 Pro | Air-gapped (QR only), open-source firmware | $149 |
| Foundation Passport | Air-gapped, fully open-source, US-made | $259 |
Tier 2: Solid Budget Options
| Device | Key Features | Price Range |
|---|---|---|
| Ledger Nano S Plus | USB-C, proven security chip | $79 |
| Trezor Safe 3 | Secure element, compact | $79 |
| Blockstream Jade | Blind oracle option, Bluetooth | $65 |
Critical Hardware Wallet Practices
1. Purchase Directly from Manufacturers
Never buy hardware wallets from Amazon, eBay, or third-party resellers. Tampered devices are documented. Order directly from:
- ledger.com- trezor.io- keyst.one- foundationdevices.com
2. Verify Device Authenticity
When your device arrives:
- Check tamper-evident packaging hasn’t been compromised- Run the manufacturer’s official verification tool- Ensure the device generates a new seed phrase (never accept pre-filled)- Verify firmware matches official releases
3. Generate Seed Phrases Offline
For maximum security with high-value holdings:
- Use an air-gapped device (Passport, Keystone) that never connects to the internet- Consider generating entropy with physical dice (Trezor and some wallets support this)- Never type your seed phrase on any internet-connected device
4. Understand the Ledger Recover Controversy
Ledger’s optional recovery service encrypts and shards your seed phrase across custodians. Our recommendation:
- For beginners worried about losing seeds: May be appropriate if you understand the tradeoffs- For privacy-conscious users: Disable completely; it creates additional attack surface- For high-value holdings: Use a wallet without this feature (Trezor, Passport, Keystone)
The fundamental tension: Ledger Recover requires the firmware to be capable of exporting seed phrases, even if you never enable the feature. Security purists consider this a design flaw regardless of implementation.
Firmware Update Best Practices
Firmware updates are necessary for security but also represent attack opportunities:
- Verify update announcements through official channels (not just email)2. Check multiple sources: Official Twitter/X, Reddit, independent security researchers3. Wait 48-72 hours for critical community review unless actively exploited4. Verify checksums if your device supports this5. Never update via links in emails—manually navigate to official sites
Seed Phrase Security: Your Last Line of Defense
Your seed phrase (recovery phrase, mnemonic) is the ultimate backup. If someone obtains it, they own your crypto. Period.
Storage Options Ranked
🏆 Best: Metal Backup + Secure Physical Storage
Metal seed phrase storage survives fire, flood, and time:
- Cryptosteel Capsule or Cryptosteel Cassette: Steel letters in steel housing- Billfodl: Stainless steel tiles- Blockplate: Stamped steel plates- DIY option: Stainless steel washers with stamped letters on a bolt
Store your metal backup in:
- Home safe (fire-rated minimum 1 hour)- Bank safe deposit box (consider jurisdiction risks)- Buried in waterproof container (extreme but effective)- Split across multiple locations (see Shamir Backup below)
✅ Good: Paper Backup with Precautions
If using paper:
- Use archival-quality paper and ink- Store in fire-resistant safe- Make multiple copies in different locations- Laminate or use waterproof pouches- Never photograph or scan
❌ Never Do This
- Store seed phrases in password managers- Email yourself your seed phrase- Store in cloud services (Google Drive, iCloud, Dropbox)- Take screenshots- Store in notes apps on your phone- Keep only one copy
Shamir Secret Sharing: Distributed Security
Shamir’s Secret Sharing splits your seed into multiple shares where only a threshold is needed to recover. For example, a 3-of-5 scheme means any 3 of your 5 shares can reconstruct the original.
Native Support:
- Trezor devices support SLIP39 Shamir Backup natively- Some software wallets support SSKR (sharded variant)
Use Case Example:
- Create 5 shares, require 3 to recover- Store shares: home safe, bank box, trusted family member, attorney, second property- No single location compromise loses your funds- No single party can access your funds alone
Important: Do not attempt DIY Shamir splitting without proper tools. Incorrect implementation creates false security.
SIM Swapping Protection: A Step-by-Step Defense
SIM swap attacks remain viable because phone carriers are soft targets. Here’s how to harden your defenses:
Immediate Actions
1. Add a PIN/Passcode to Your Carrier Account
| Carrier | How to Add |
|---|---|
| Verizon | My Verizon app → Account → PIN |
| AT&T | myAT&T app → Account security → Extra Security |
| T-Mobile | Account settings → Security → SIM Protection |
| International | Contact carrier directly |
2. Remove SMS-Based 2FA Everywhere Possible
Prioritize removing SMS 2FA from:
- Cryptocurrency exchanges (Coinbase, Kraken, Gemini, etc.)- Email accounts (this is critical—email resets everything)- Financial accounts- Social media (used for social engineering reconnaissance)
3. Use Hardware Security Keys
Replace SMS 2FA with FIDO2/WebAuthn hardware keys:
- YubiKey 5 Series: Gold standard, multiple form factors ($50-75)- Google Titan: Budget-friendly alternative ($30-35)- Trezor: Your hardware wallet can also serve as a security key
Register at least two hardware keys for each critical account. Store the backup key separately.
4. Use Authenticator Apps as Fallback
When hardware keys aren’t supported:
- Aegis (Android, open-source): Best option- Raivo (iOS): Privacy-focused- Google Authenticator: Widely compatible- Authy: Avoid—cloud sync creates vulnerabilities
Advanced Protections
Port Freeze/Number Lock
Some carriers offer the ability to completely lock your number against porting:
- Verizon: “Number Lock” feature- T-Mobile: “SIM Protection”- Ask your carrier about their strongest available protection
Use a Separate Phone Number for Crypto
Consider maintaining a dedicated phone number exclusively for cryptocurrency accounts:
- Prepaid SIM registered with minimal information- Or VoIP number (Google Voice, MySudo) for accounts that require phone verification- Never use this number for anything else- Store the SIM separately from your main phone
Number Privacy
- Don’t publicly share your phone number- Use burner numbers for online forms- Be aware that data breaches may have already exposed your number
Hot Wallets vs. Cold Storage: Finding Your Balance
The eternal question: convenience vs. security. Here’s a practical framework.
The Tiered Approach
Tier 1: Hot Wallet (5-10% of Holdings)
- Funds you actively use for transactions- Mobile or browser wallet- Accept higher risk for convenience- Never store more than you’d be upset to lose
Recommended hot wallets:
- Rabby: Excellent security warnings, transaction simulation- MetaMask: Most compatible, use with hardware wallet integration- Rainbow: Beautiful UX, good for Ethereum ecosystem- Phantom: Solana ecosystem standard
Tier 2: Warm Storage (10-20% of Holdings)
- Hardware wallet connected to computer when needed- Used for regular but not daily transactions- Medium-term holdings
Tier 3: Cold Storage (70-85% of Holdings)
- Air-gapped hardware wallet or dedicated device- Long-term holdings- Rarely accessed- Consider multi-sig (see below)
Hot Wallet Safety Practices
Even for “spending money,” follow these rules:
- Enable all available security features: Biometrics, spending limits, transaction simulation2. Revoke unused token approvals: Use revoke.cash regularly3. Be skeptical of all transaction requests: Verify addresses character-by-character4. Use a dedicated browser: Don’t browse random sites with your wallet extension active5. Consider wallet isolation: Different wallets for different risk activities (DeFi vs. receiving payments)
The Air Gap Advantage
For maximum cold storage security, consider fully air-gapped devices that never connect to the internet:
Keystone 3 Pro / Foundation Passport:
- Communicate only via QR codes- Cannot be remotely compromised- Physical verification of all transaction details- Slightly less convenient but dramatically more secure
Air-Gapped Laptop Setup:
- Dedicated laptop with WiFi hardware physically removed- Running Bitcoin-only software (Sparrow, Specter)- Transactions passed via SD card or QR- Overkill for most users but viable for high-value Bitcoin storage
Multi-Signature Security for High-Value Holdings
If you hold significant cryptocurrency value (generally $100,000+), multi-signature wallets provide protection that single-signature cannot match.
How Multi-Sig Works
A multi-sig wallet requires multiple private keys to authorize transactions. Common configurations:
- 2-of-3: Any two of three keys required. Good balance of security and recovery.- 3-of-5: Any three of five keys. Higher security, more complex management.
Multi-Sig Solutions in 2026
Bitcoin-Focused:
| Service | Model | Starting Price | Best For |
|---|---|---|---|
| Casa | 2-of-3 to 3-of-5 | $120/year | Premium experience, concierge support |
| Unchained | 2-of-3 | $250/year | Collaborative custody, financial services |
| Sparrow + Hardware Wallets | Self-managed | Free (hardware costs) | Technical users who want full control |
| Nunchuk | Self-managed | Free tier available | Mobile-friendly multi-sig |
Ethereum/EVM:
| Service | Model | Fees | Best For |
|---|---|---|---|
| Safe (Gnosis Safe) | Configurable | Gas only | Most established, widely integrated |
| Argent | Social recovery | Gas only | Mobile-first with guardian system |
| Kernel | Smart account | Gas only | Account abstraction features |
Multi-Sig Best Practices
- Geographic distribution: Store keys in different physical locations2. Device diversity: Use different hardware wallet brands for each key3. Documentation: Clear instructions for your heirs or backup keyholders4. Test recovery: Actually test reconstructing the wallet from backups5. Key ceremony: When creating, ensure proper entropy and no single point of failure
When Multi-Sig Might Not Be Worth It
- Holdings under $50,000 (complexity may exceed benefit)- Very active trading (signing friction becomes costly)- Users who struggle with single-sig security (multi-sig won’t fix bad practices)
Crypto Insurance Options for Retail Holders
A growing market now offers protection against various loss scenarios.
Decentralized Insurance Protocols
Nexus Mutual
- Covers smart contract failures, exchange hacks, protocol failures- Staking-based mutual model- Claims assessed by member vote- Cannot cover private key loss (no way to verify)
InsurAce
- Multi-chain coverage- Portfolio-based pricing- IDO, bridge, and stablecoin depeg coverage
Risk Harbor / Neptune Mutual
- Automated claims for specific events- Parametric triggers (no claims process for covered events)
Limitations:
- Decentralized insurance cannot cover personal security failures- Private key compromise is uninsurable (moral hazard)- Coverage limits may be well below your holdings- Claims processes can be contentious
Custodial Options with Insurance
If you’re comfortable with custodial solutions, some offer insurance:
- Coinbase: Holds insurance on custodied crypto (crime coverage)- Gemini: FDIC insurance on cash, crime insurance on crypto- Kraken: Maintains reserves but disclosure on insurance is limited- BitGo: Offers institutional custody with $250M+ insurance
Tradeoff: You’re trusting the custodian with your private keys. This protects against some risks (personal security failures) while introducing others (custodian failure, regulatory seizure).
Self-Custody Insurance Challenges
The fundamental problem: insurance providers cannot distinguish between genuine theft and staged theft. If you claim someone stole your keys, there’s no way to prove you didn’t transfer funds yourself.
Practical solutions:
- Multi-sig with institutional co-signer (Unchained, Casa) provides some coverage through the service- Time-locked transactions and social recovery provide loss prevention rather than insurance- Diversification across custodians and self-custody reduces single-point-of-failure risk
Operational Security (OpSec) Essentials
Beyond technical measures, your behavior patterns determine your security.
Digital OpSec
1. Dedicated Devices
- Consider a separate phone/computer for crypto activities- Minimize installed apps and browser extensions- No gaming, torrenting, or risky browsing on crypto devices
2. Email Security
- Use ProtonMail or Tutanota for crypto accounts- Unique email address for each major exchange- Never use your crypto email for anything else
3. Password Hygiene
- Unique, strong passwords for every crypto service- Use Bitwarden or 1Password (not LastPass after their breaches)- Enable 2FA on your password manager (hardware key preferred)
4. Network Security
- VPN for all crypto activities (Mullvad, ProtonVPN recommended)- Never access wallets on public WiFi without VPN- Consider dedicated home network for crypto devices
Physical OpSec
1. Don’t Advertise Wealth
- Avoid crypto-branded clothing, stickers, license plates- Don’t share specific holdings on social media- Be vague about crypto involvement with strangers
2. Home Security
- If holding significant value, consider home security system- Distribute backup materials across locations- Consider how someone might access your seed phrase under duress
3. Travel Considerations
- Don’t travel with primary hardware wallets- If traveling with crypto access, use separate device with limited funds- Be aware of border search powers in various jurisdictions
4. Plausible Deniability
- Consider having a “decoy” wallet with small balance- Passphrase/hidden wallet features allow multiple wallets from one seed- Know what you would do in a physical duress situation
Your Personal Wallet Security Checklist
Use this checklist to audit your current setup:
Hardware & Devices
- Hardware wallet purchased directly from manufacturer- [ ] Device authenticity verified- [ ] Firmware updated to latest stable version- [ ] PIN set (not obvious numbers)- [ ] Passphrase enabled for hidden wallet (optional, for advanced users)
Seed Phrase Security
- Seed phrase stored on metal backup- [ ] At least two copies in separate physical locations- [ ] No digital copies exist anywhere- [ ] Tested recovery process on separate device- [ ] Shamir backup implemented (for high-value holdings)
Account Security
- SMS 2FA removed from all crypto accounts- [ ] Hardware security key set up on exchanges and email- [ ] Unique passwords for all crypto services- [ ] Carrier account PIN enabled- [ ] Email used for crypto is separate and secured
Software & Network
- VPN used for all crypto activities- [ ] Browser extensions minimized on crypto browser- [ ] Token approvals reviewed and revoked quarterly- [ ] Transaction simulation enabled (Rabby or similar)- [ ] Dedicated device or profile for crypto (ideal)
Multi-Sig & Insurance (High-Value Holders)
- Multi-signature wallet implemented ($100k+)- [ ] Keys stored in geographically separate locations- [ ] Recovery process documented for heirs- [ ] Insurance coverage reviewed (if available)
OpSec & Behavior
- No public discussion of specific holdings- [ ] Crypto-related data minimized in breach databases- [ ] Physical security plan for high-value scenarios- [ ] Duress/coercion scenario considered- [ ] Regular security review scheduled (quarterly)
Final Thoughts
Personal crypto security in 2026 requires ongoing vigilance. The attacks have grown more sophisticated, but so have the defenses. The fundamentals haven’t changed: secure your seed phrase, eliminate single points of failure, and assume that attackers are watching.
The good news is that following even the basic practices in this guide puts you ahead of most holders. Attackers prefer easy targets. Don’t be one.
Start with the highest-impact items: get a hardware wallet if you don’t have one, move your seed phrase to metal backup, and eliminate SMS 2FA from critical accounts. Build from there based on the value of your holdings and your personal risk tolerance.
Your cryptocurrency security is ultimately your responsibility. No exchange, wallet provider, or protocol can protect you from yourself. Take that responsibility seriously, and you’ll navigate the evolving threat landscape successfully.
Have questions about securing your crypto holdings? Join the Crypto Impact Hub community for ongoing security discussions and updates.